
[ad_1]
Once again we look back at the past year in cybercrime and those who we lost… to the law. This year was no different to last: We saw another round of high-profile busts, arrests, sanctions and prison time for some of the most prolific cybercriminals in recent years.
This is our look back at who got nabbed or otherwise busted, featuring: why a Russian accused of ransomware burned his passport, which notorious malware gang reared its ugly head again and why one country’s hackers targeted an unsuspecting phone maker.
For a time, Joseph James O’Connor was one of the internet’s most wanted hackers, not just by the feds investigating the breach, but for the curious public who watched his hack play out in real time.
O’Connor was a member of the hacking group that broke into Twitter to abuse access to an internal admin tool they used to hijack high-profile Twitter accounts, including Apple, Joe Biden and Elon Musk (who went on to buy the site) to spread a crypto scam. Twitter took drastic measures to rid the hackers from its network by temporarily blocking all of the site’s 200-million-plus users from posting.
A New York judge sentenced the 24-year-old hacker to five years in prison, two of which O’Connor already served in pre-trial custody.
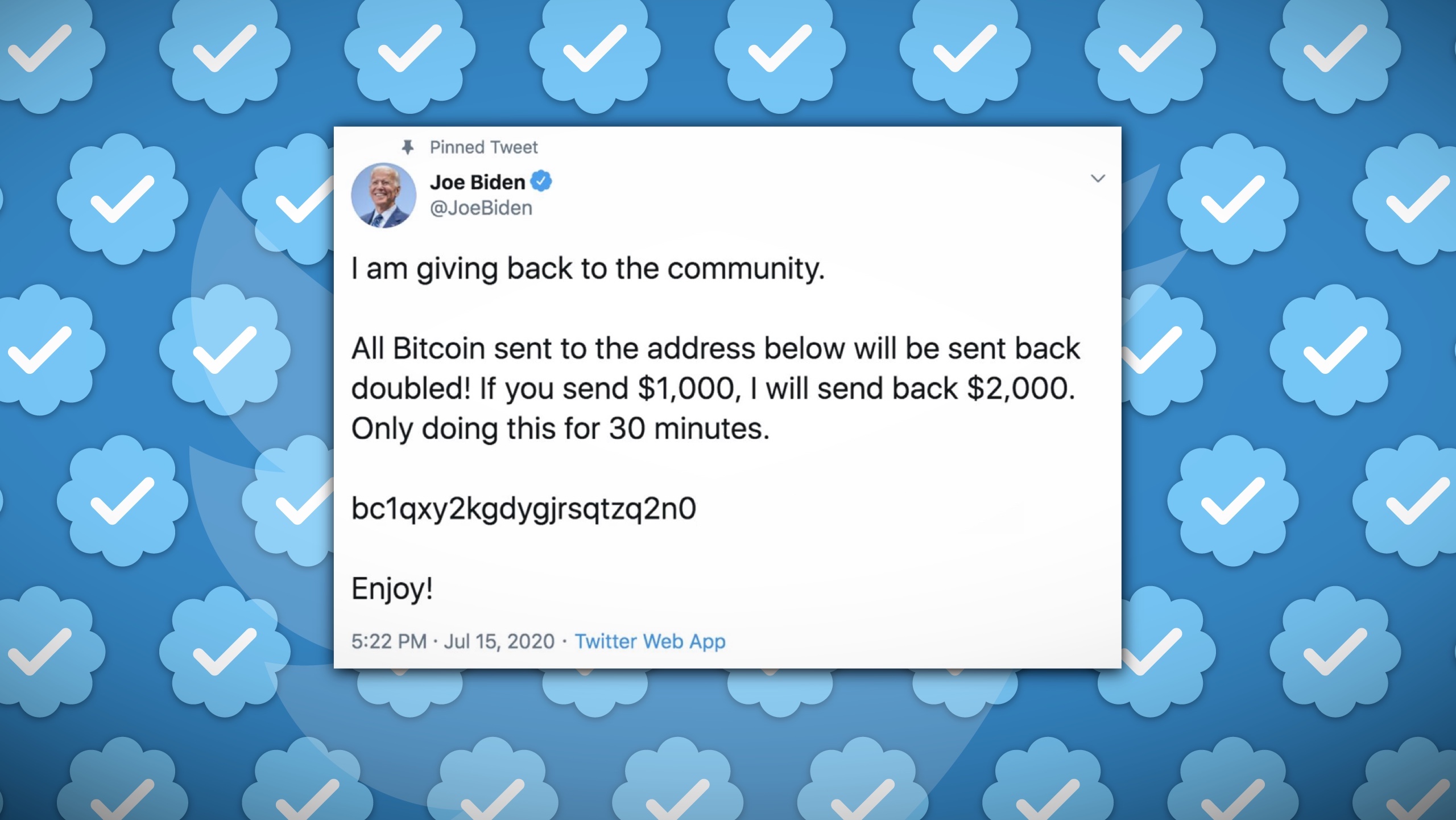
A screenshot of a tweet from Joe Biden’s briefly hacked Twitter account displaying a crypto scam. Image Credits: TechCrunch
Federal prosecutors this year accused a former Amazon employee of hacking into a cryptocurrency exchange and stealing millions’ worth of customers’ crypto. The case appeared at first as an ethical hacker turning rogue by apparently offering to return the funds in return for a bug bounty. But ultimately Shakeeb Ahmed was caught out in part by Googling his own crimes that prosecutors say related to “his own criminal liability.”
In the end, Ahmed pleaded guilty earlier in December, according to the Justice Department, and faces up to five years in prison — and paying back $5 million to victims.
Why did a Russian man accused by U.S. prosecutors of ransomware attacks burn his passport? According to the accused hacker, Mikhail Matveev, it’s because U.S. government charges would follow him anywhere he went and most countries would extradite him for the crimes he’s accused of — crimes he hasn’t denied, per se, but rather outwardly embraced. In an interview with TechCrunch, Matveev said the last time he traveled was to Thailand in 2014, but not since.
Federal prosecutors say Matveev is a “central figure” in developing and deploying the Hive, LockBit and Babuk ransomware variants, which have resulted in millions of dollars’ worth of ransom payments. Matveev is believed to live in the Russian enclave of Kaliningrad, where he remains tantalizingly close yet just out of reach of the authorities.

The FBI’s wanted poster for Mikhail Matveev. Image Credits: FBI
Hackers for the hermit kingdom were busier than ever this year, racking up hacks on popular crypto wallets and major crypto projects with the aim of making as much money for the regime from anywhere it can get it to fund its sanctioned nuclear weapons program.
Some of the cyberattacks linked to North Korea might not have made much sense on the face of it, but breaking into software companies gave the hackers access to the targets they were after. Enterprise phone provider 3CX said that North Korean hackers broke into its systems and planted malware in a tainted software update that rolled out to customers in a long-game effort to target 3CX’s crypto customers. Software company JumpCloud said it too was hacked by North Korean hackers, likely in an effort to gather data on a handful of its crypto-related customers.
The FBI warned earlier this year that North Korean hackers were readying to cash out some of their recent crypto heists.
It took the feds about a decade but their persistence paid off when they finally identified the mastermind behind Try2Check, a credit card checking operation that allowed criminals who buy credit card numbers in bulk to identify which cards are still active. The scheme earned the Russian national, Denis Gennadievich Kulkov, more than $18 million in illicit proceeds — and a place on the U.S. Secret Service’s most wanted list with a $10 million bounty for information leading to Kulkov’s conviction. That might not be any time soon, given Kulkov remains in Russia and squarely out of the hands of U.S. prosecutors.
A prolific hacker and seller of stolen data, the administrator of the cybercrime forum BreachForums known as Pompompurin, was busted on home turf by the FBI in a leafy town in upstate New York. BreachForums for a time was involved in the sale of millions of people’s data with more than 340,000 active members, to the point where the Justice Department sought to “disrupt” the site to knock it offline. The operation saw the arrest of Conor Brian Fitzpatrick, 20, following an extensive surveillance operation. In the end it wasn’t just charges of computer hacking and wire fraud that brought down the notorious hacking forum administrator, but also possession of child abuse imagery. Fitzpatrick subsequently pleaded guilty and will be sentenced at a later date.
Qakbot was one of the longest-running and high-profile hacking groups of the past decade, and once the malware-of-choice for delivering ransomware to companies, organizations and governments around the world, generating tens of millions of dollars in ransom payments. At its peak, the FBI said Qakbot had compromised more than 700,000 devices as of June 2023, with at least 200,000 hacked devices located in the United States. In a daring effort to knock the malware offline for good, the FBI launched Operation Duck Hunt (don’t say that too quickly), which tricked Qakbot-infected computers into downloading an FBI-made uninstaller, ridding the malware from the infected device. The operation was hailed as a success. But recent Qakbot infections suggest that the takedown was little more than a short setback.
In what is likely the last cyber-related conviction of the year: A hacker accused of involvement with the prolific Lapsus$ hacking group will be detained until doctors determine he no longer poses a threat to the public. Arion Kurtaj, a teenager from Oxford, was sentenced to an indefinite hospital order in December, reports the BBC. Kurtaj is one of several hackers who raided Rockstar Games, Uber, Nvidia and telecom giant EE who used social engineering and threats to score access to corporate networks. The judge said the teenager’s skills and desire to continue committing cybercrime meant he remains a high risk to the public.
Read more on TechCrunch:
[ad_2]
Source link





